Publish New CRL From an Offline Root CA
If you’ve been following best practices, you likely have a multi-tiered Microsoft PKI with an offline root CA. In this case you’ll have to publish a new Certificate Revocation List using your offline CA server and install this on your online CA server. The following article outlines the steps involved in completing this process.
Generating the new CRL Using the Offline CA
First, you’ll need to power up your offline CA. Once it’s finished booting, navigate to C:\windows\system32\certsrv\certenroll and rename your current CRL (filename may vary, but should be the only file in this folder with a *.crl extension) to *.crl.old.
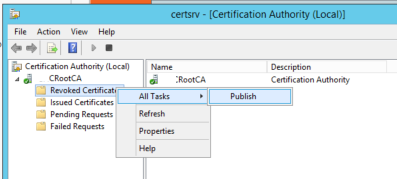
Now under Administrative Tools open the Certificate Authority management console. Once this has loaded, right-click on the Revoked Certificates folder and choose All Tasks > Publish. Select New CRL from the next prompt that appears.
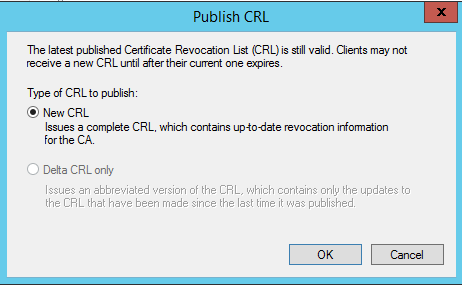
This will generate a new CRL file in the same location as the one we just renamed (C:\windows\system32\certsrv\certenroll\yourfilename.crl), we need to copy this somewhere that will be accessible from the online CA server.
Once you’ve copied the CRL file somewhere accessible, you can shut down the offline CA server again.
Publishing the new CRL in Active Directory
We now need to log onto our online CA server and copy the new CRL file to C:\windows\system32\certsrv\certenroll. Once you’ve copied the file here we need to open command prompt as an administrator and run the following command: Certutil -v -f -dsPublish "c:\windows\system32\certsrv\certenroll\yourfilename.crl"
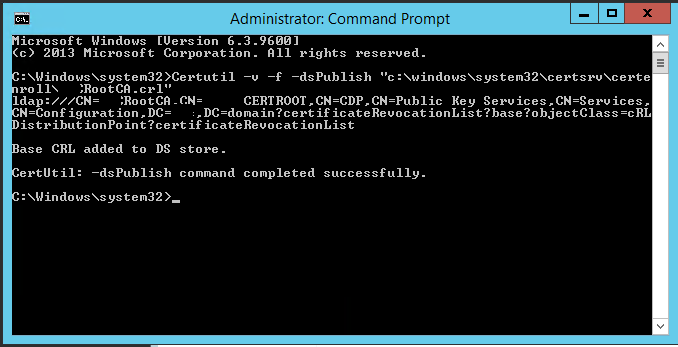
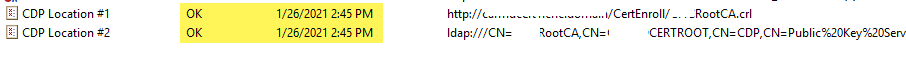
We should see a message as above stating that the dsPublish command completed successfully. We can verify this by opening MMC on the online CA, loading the Enterprise PKI snap-in and selecting our Root CA name (offline root).
Verify that CDP locations 1 and 2 are showing with a status of OK and that the expiration date is X weeks ahead of the current date (this date will depend on the periods you configured when installing your PKI servers).